Why MFA Isn’t Optional Anymore
What if a password your team hasn’t used in years could still access your business?
That’s exactly what happened in a recent cyber incident. No sophisticated hacking. No warning signs. Just old login details that were never turned off.
A cybersecurity investigation uncovered a campaign where sensitive data from dozens of businesses worldwide was quietly stolen and sold. Different industries, different countries — but one shared weakness.
Access to critical cloud systems relied on username and password alone. No second verification step.
The attackers used infostealing malware to quietly collect saved passwords from infected devices, including personal and home computers. Some of those stolen passwords weren’t used immediately. In fact, many were years old.
That revealed two major issues:
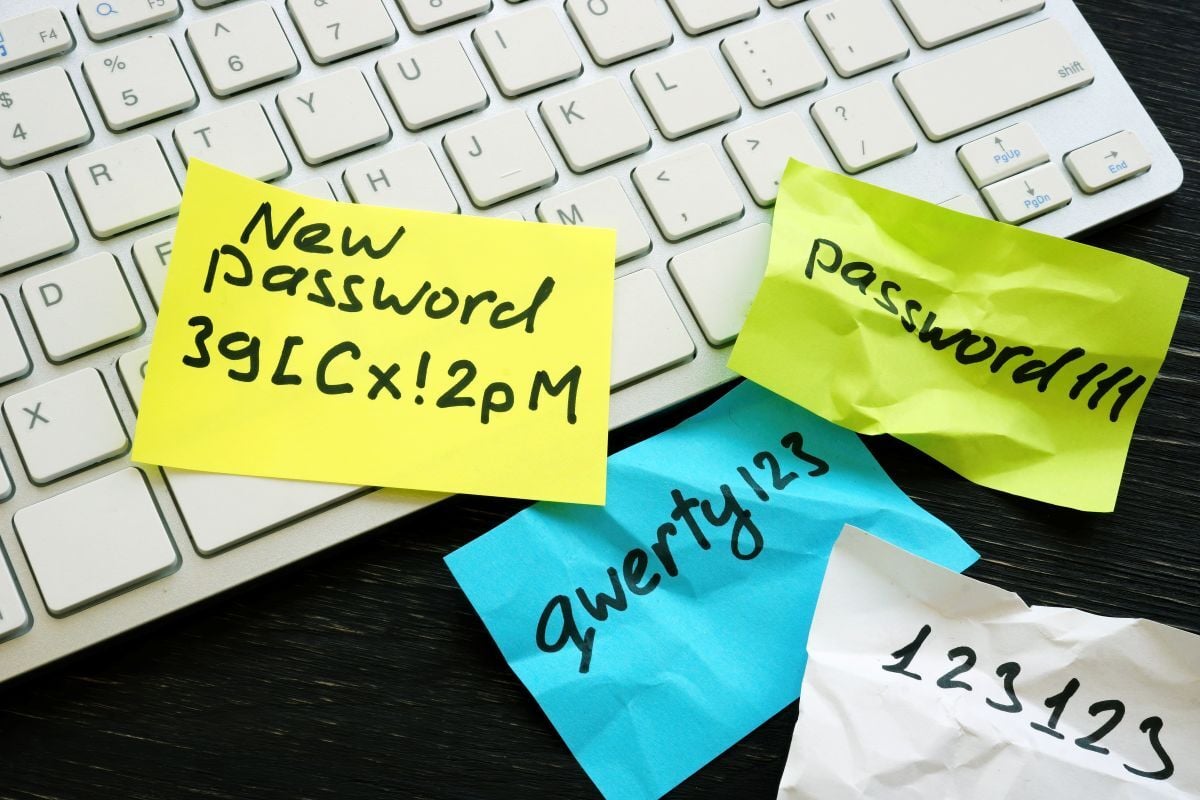
- Passwords weren’t changed often enough
- Old logins were still trusted long after they should have been disabled
This is a “latency” problem — old compromises don’t expire just because time passes.
Every one of these attacks could have been stopped with multi‑factor authentication (MFA). The attackers had the passwords, but not the second factor — no phone, no app, no approval.
Yes, MFA adds a small extra step. But it turns stolen passwords into useless data.
Old passwords don’t protect themselves. One extra lock makes all the difference.
Need help enforcing MFA? Contact us today!